I’ve noticed an interesting trend in the comment spam I’ve been getting (luckily few of it gets through).
There seems to be three basic categories …
Continue reading
I’ve noticed an interesting trend in the comment spam I’ve been getting (luckily few of it gets through).
There seems to be three basic categories …
Continue reading
 I’ve decided to stop reporting spam to ISP’s.
I’ve decided to stop reporting spam to ISP’s.
It just seems like an incredible waste of effort on my part.
For YEARS now I’ve used SpamCop to report spam to ISP’s (both the mail provider and related web hosts) and have gotten very few non-automated responses.
![]() A few days ago I discovered that Yahoo had created a email abuse feedback loop system.
A few days ago I discovered that Yahoo had created a email abuse feedback loop system.
Based on my experiences with AOL’s feedback system, I really didn’t have high hopes for Yahoo’s efforts … but decided to give it a shot anyways.
I signed up to get abuse reports for midrange.com messages. It took a bit of time to get it all processed, but it’s now in place.
The next day I got my first report of abuse.
 I’ve never understood the rationale behind the various web scripts that claim that they are ‘poisoning’ spammers lists.
I’ve never understood the rationale behind the various web scripts that claim that they are ‘poisoning’ spammers lists.
They claim that, by putting a bunch of garbage email addresses on a web page and encouraging spammers to harvest the page, they are poisoning a spammers email list and thus making the list useless so that they will discard the list.
Where did they ever get the idea that spammers CARE about the good & bad addresses that they harvest. Considering how much it costs them to send spam, they wouldn’t are one lick if 90% of the addresses on their list is valid or not. Especially since most spam sent these days is done by infected personal computers controlled by ‘bot herders‘.
I often watch the log file on my mail server … and observe the servers trying to deliver mail to mangled and non-existent addresses. It’s clear the sending system is just blasting names at my server without any consideration if the address exists or not. My mail server software (sendmail) had an option to throttle the connection of any system that gets more than a certian number of bad addresses. I also have a script that monitors for that behavior and adds a firewall rule to completely block such systems.
My advice to those who create such scripts … focus your energies elsewhere … right now you’re just wasting your time.
Oh, by the way, for those of you who are trying to use “User-Agent” lists to block harvesters … don’t waste your time on that either. Harvesters, like spammers, will never clearly identify themselves as such … and will use a completely legitimate user agent when spidering your website. Additionally, they will absolutely ignore any robots.txt file that you have in your site.
There are, however, systems that use a somewhat similar technique to stop spammers … but are much more effective. Instead of just trying to poison a spammers list … they use traceable email addresses. This means that, when a harvester visits a page with this traceable email address, they log the IP the harvester is using and the email address that is harvested. This way, when spam is sent to the address, they know when and how the address was harvested and where it was sent from. Theoretically the spammer is reported both to the ISP that the mail was sent through AND the ISP that was used to harvest the address. Project Honeypot is one such anti-harvester organization.
Recently I noticed that there’s a lot of temporary files in the /tmp directory on my mail server … all the files have spamassassin in the file name. I figured that in some cases, SpamAssassin (or programs it calls) isn’t cleaning up properly.
I whipped up this script that will clean up any spamassassin files & directories that are older than a set number of minutes (60 in my case)…
#!/bin/sh
AGE=60
if [ "$1" == "--test" ]
then
CMD="-exec echo"
echo "$0: test mode"
else
CMD="-exec"
fi
/usr/bin/find /tmp \
-mmin +$AGE \
-name spamassassin.ocr* \
$CMD /bin/rm -f '{}' \;
/usr/bin/find /tmp \
-maxdepth 1 \
-mmin +$AGE \
-type d \
-name .spamassassin\* \
$CMD /bin/rm -rf '{}' \;
If you run the script with a parameter of ‘–test’, it will just show the commands it would have executed.
I put the script in /etc/cron.hourly directory so it gets executed every hour.
Today … like most days … I received phishing spam … nothing new about that.
Just out of idle curiosity, I clicked on the link they indicated (a bogus E*Trade site) to see what it looked like … this is a screen shot of what I saw …
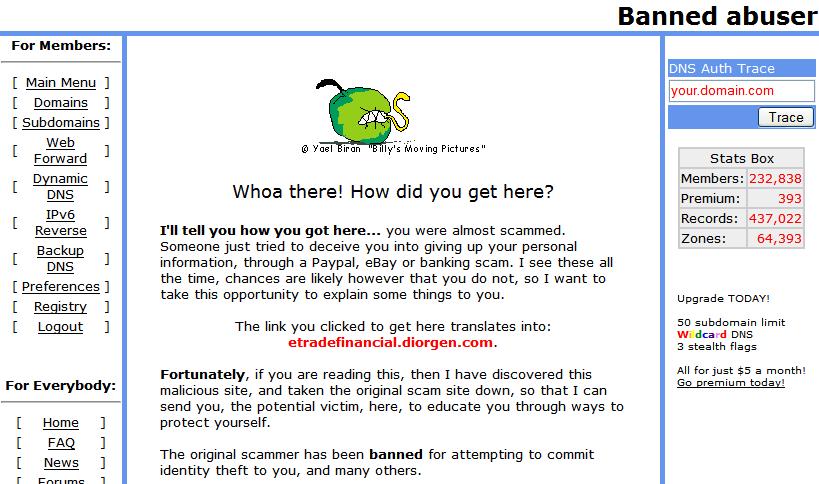
I have to tip my hat to Joshua Anderson, who runs afraid.org … his response to the phishing attempt was absolutely the best thing that could be done.
I wish other service providers responded in similar fashion.
[tags]phishing, spam, security, isp, tos[/tags]
For a while I’ve been using limited greylisting on my mail server with reasonably good success.
Last weekend I implemented site wide and I have to say the results are dramatic. The amount of spam (even low rated by spamassassin) has dropped off significantly.
Detailed information on greylisting can be found here, but in a nutshell:
Greylisting relies on the fact that spammers don’t use normal mail servers. Basically, the first time a mail server receives a mail delivery request, it responds with a soft failure … with a message indicating that greylisting is in effect and they should retry the delivery in certain amount of time (this is a human readable message, not machine readable). Since normal mail servers will accept this message and requeue the email for delivery, the email will then be delivered normally (probably on the next pass).
Spammers aren’t that persistent, so they just go on to their next target.
A good greylisting implementation retains the list of servers that have successfully delivered in a whitelist, so the next time they try to deliver there is no delay, the delay is only encountered once.
One downside of greylisting that I’ve found is that there is an increased chance of messages arriving out of order when a server tries it’s first message deliver. The reason is this … the first message delivery will be attempted and be rejected due to greylisting, if a different message delivery is attempted AFTER the greylisting delay has expired but BEFORE the first message is delivered, then the second message will be delivered and will be out of context.
I’ve got my mail server configured to greylist servers for only 2 minutes … so the next time the server tries to deliver, it’s almost certain to be successful.
I’m using milter-greylist with sendmail. It was easy to setup and works great.
[tags]spam, sendmail, greylisting, milter[/tags]
 I’m wondering if anyone has actually gotten a satisfactory response from a major ISP after sending a report to their abuse department?
I’m wondering if anyone has actually gotten a satisfactory response from a major ISP after sending a report to their abuse department?
I’ve submitted a large number of abuse reports to SBC, Comcast, RoadRunner, etc … but have yet to get any satisfactory response at all. One report I submitted to SBC, via DSLReports SBC Direct forum got me some grief because they wanted me to Opt out first. My opinion, of course, was that I should never have been Opted In involuntarily in the first place.
A week or so ago I got an email from GoDaddy, my domain registrar, about a abuse report that was mistakenly reported against midrange.com … and they demanded a response within 24 hours … which I gave them (it was a total misunderstanding … someone was reporting spam against someone else hosted by GoDaddy … but the email they forwarded was misconstrued to be coming from midrange.com). Even though I responded well within the 24 hours they specified (I responded within 24 minutes), they did not respond back to me for more than a week. I had to send 3 requests for a response to get them to reply.
I guess the two questions I would like to see answered are …
My own experience is no to both.
[tags]Spam, email, ISP[/tags]
The federal government’s two-year-old anti-spam law is helping to cut back on unsolicited bulk e-mail, but more must be done to fight the problem. Those are the conclusions of a Federal Trade Commission report, released today, on how well the law is working.
– ABC News — Spam Slayer: FTC’s CAN-SPAM Report Card
Uh yeah … right.
I think the FTC needs to take a good long hard look at the internet again and rethink their statement.
CANSPAM did absolutely nothing … because the people sending spam are totally unconcerned about the laws of the U.S.
The spam my server receives has only INCREASED in the last year.
And, as long as the internet is unregulated, the spam will only continue to increase.
Please note: I am NOT advocating regulation of the internet.
If the government wants to put some legislation in place to help combat spam … put some penalties on running open relays, open proxies, and failure to implement anti-virus & anti-worm technologies on computers.
[tags]Spam, Government, FTC[/tags]
The first sign that a email message is spam: They assure you that it is not spam.
This is an official notification of the availability of a package deposited in your name and it is not a sales solicitation or SPAM.